The introduction of the Cybersecurity Maturity Model Certification (CMMC) was lauded by many as a significant step towards improving national security; others loathed the new regulations for the excessive cost and other barriers to being awarded a government contract.
“The original CMMC program mandated implementation in 2025; however, on November 4, 2021 the DoD announced CMMC2 revisions, simplifying tiering and audit requirements. Sudden program changes left many questioning the impact and the ability to adhere to a regulation with moving requirements.”
The When
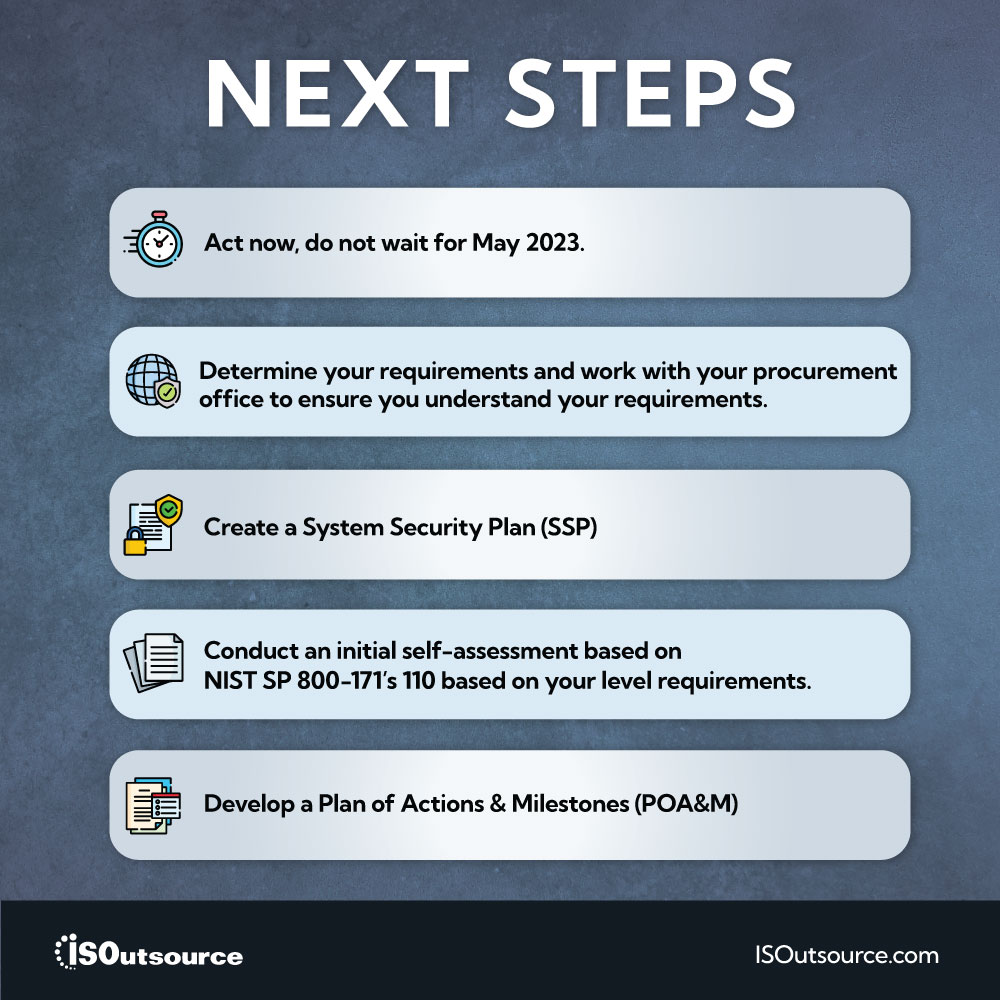
The original CMMC original was cancelled immediately upon being placed in the Federal Register in November 2021, effectivity creating the official path for CMMC2. The Interim Rule implementing CMMC framework is expected to be released in May 2023 by the DoD. CMMC2 requirements are expected to appear in DoD contract by July 2023, 60 days after the Interim Rule publication.
Why the change?
Significant program changes occurred after Deputy Secretary of Defense, Kathleen Hick, directed the Department of Defense to review the CMMC program and evaluate if the program was achieving its goals without creating unnecessary barriers for defense contractors. The review included over 1,000 interviews and 850 public comments.
Who was impacted?
CMMC2 Leven 1 and 2 only impact government contractors and subcontractors with the CMMC contract clauses. Contract language will stipulate level (1-3) and audit requirements.
- If you have a contract with original CMMC requirements, contact the procurement agency to validate new CMMC2 requirements.
- If you are seeking a contract, verify the language or requirements.
- If you were discouraged from seeking a government contract because of the requirements, I recommend you revisit the opportunity to see how CMMC2 improves the opportunity.
What changes between the original CMMC and CMMC2?
In simple terms, CMMC2 has only 3 levels compared to the original 5 levels and audit requirements are significantly reduced. Other high-level changes include:
- Official CMMC2framework is expected May 2023, organizations should follow National Institute of Standards and Technology (i.e., NIST SP 800-171, NIST SP 800-172) until that point.
- A formal self-certification processes when third-party assessment is not required.
- Plans of Action and Milestones (POAMs) with waivers create program flexibility.
- Suspension of piloting efforts and the postponement mandatory compliance until the completed ruling of 32 CFR (CMMC definitions) and 48 CFR (procurement code).
Additional Level Details
- Level 1 Foundational – remains the same as the original CMMC program, it focuses on the protection of FCI Federal Contract Information (FCI). Compliancy requires implementing 17 basic security practices, which is already a requirement under FAR 52.204-21, “Basic Safeguarding of Contractor Information Systems”. This includes the subset of NIST SP 800-171. Typically, Level 1 contractors do not process, store, or transmit CUI, but do process, store, or handle FCI. Self-assessments are required accompanied by a senior company official attestation.
- Level 2 Advanced – focuses on companies with Controlled Unclassified Information (CUI). It includes the implementation of all NIST SP 800-171 (with the exceptions of POA&Ms and waivers) 110 practices; this is a reduction of 20 security requirements. Two assessment options exist based on the classification of national security information. Option 1: Self-assessments are required accompanied by a senior company official attestation. Option:2 triannual assessments by a Certified Third-Party Assessment Organization (C3PAO).
- Level 3 Expert – focuses on Advanced Persistent Threats (APTs) and companies working on CUI for DoD high priority programs. It includes the implementation of all NIST SP 800-172 (with the exceptions of POA&Ms and waivers) 110+ practices. The actual requirements are expected to be release in May 2023 with immediate implementation requirements. Level 3 contractors will undergo government-led cybersecurity and compliance assessments.
Resources